Describing the problem – What happens if PII is stored as plain text?
Many businesses that build software application today are required by the GDPR regulations to protect the stored sensitive data. We might refer to sensitive data as PII (personally identifiable information), and keeping this sensitive data as plain text in configuration files / databases represents a huge risk as they can be visible to anyone that has access to the deployment servers.
Some businesses took a step further and started to encrypt the sensitive data, but they would keep the encryption key hardcoded within the application. Now let’s take a step back and see what is an encryption key and how does it sit within the encryption process by following the below diagram:
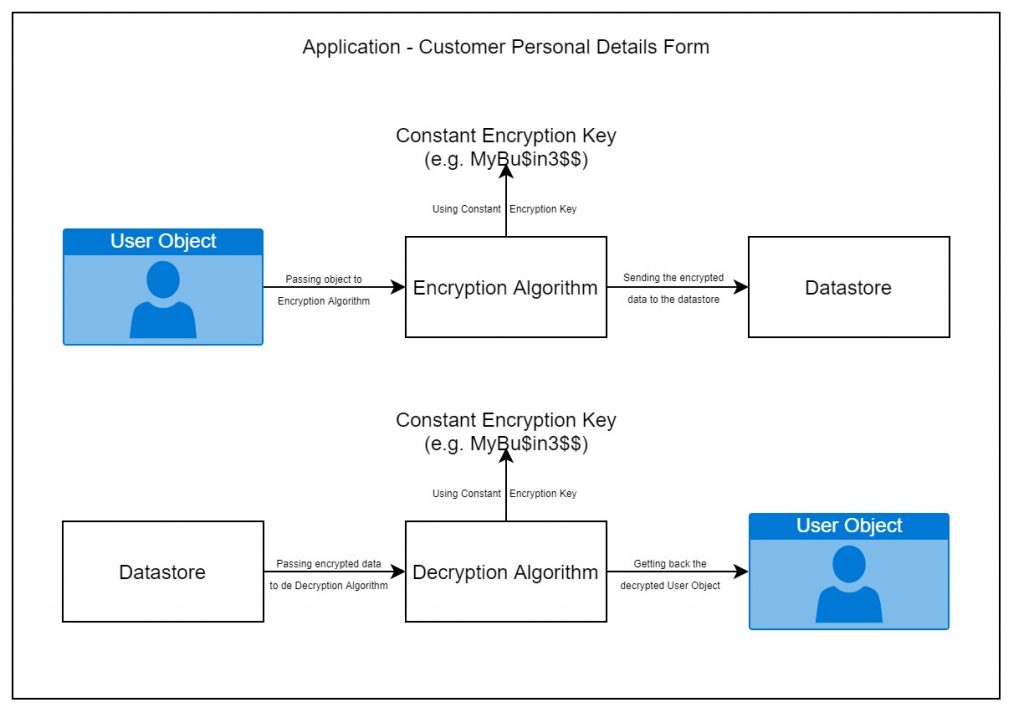
Quite simple isn’t it? But again, storing the encryption key within the application still represents a huge risk for the business and the key can be used again, by anyone that has access to the deployment servers to decrypt the data from the datastore.
Sometimes, the businesses security policy demands that the encryption key to be renewed frequently (rolling), which again, using a similar approach like the one described above would add even more complexity by changing the hardcoded key, create a new deployment of the application, etc.
Solution – How can PII can be stored more securely
Lets try to solve the problem step by step by summarizing the problem and asking the right questions. Lets start with, again:
What is the problem?
Well, we have two:
- the fact that we use the same encryption key every time when we want to encrypt data
- the encryption key does not expire, unless someone sets an alarm every 30 days to change it and redeploy the application
These problems are raising some other problems:
- How can we have a new encryption key each time when we want to encrypt data?
- How do we force encryption keys expiration?
- How do we decrypt the data if the encryption key expired?
Because I love drawing diagrams, lets consider the following solution for the problem number one:

Now we have an unique encryption key every time when we encrypt data, perfect! We can get rid of the constant encryption key, but we still have a problem, how do we know to query the right encryption key for an user? Lets follow the next diagram:

Leave a Reply